To make life harder for criminals who aim to steal/misuse your online accounts or identity, 2FA (Two factor authentication) / MFA (Multi factor authentication) is a great place to start.
A little background on SFA/2FA/MFA?
What is 2FA (Two factor authentication) / MFA (Multi factor authentication)? According to Wikipedia authentication factors can be:
- Something the user knows (and only the user knows)
- Something the user has (and only the user has)
- Something the user is (and only the user is)
So for example:
- Could be a password
- Could be an security token
- Could be a fingerprint or retina scan or something else
2FA is basically a combination of two of the above factors. Multi factor authentication can be a combination of 2 factors, or 3, or etc.
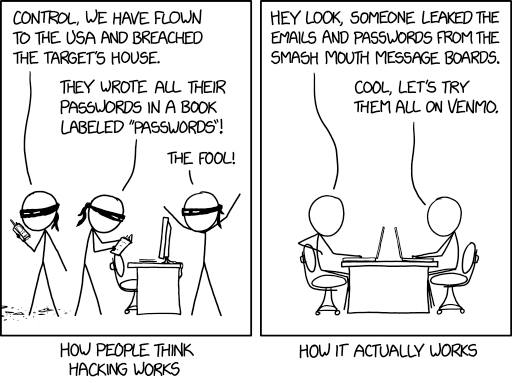
The absolute worst you can have is a SFA (Single factor authentication). If this is the case your account is vulnerable to a number of attacks. Brute forcing/ dictionary checking is one of the most used attacks. A lot of people still use an easy, dictionary based password that is used for different services or sites. I will not go into detail on this problem but it happens. A lot!
There are all kinds of 2FA available. The best known 2FA compose of:
- SMS token
- Authenticator app (approval based sign in or OTP (one time password))
- Hardware security token
A list of pros and cons of each of those can be found here.
The hardware security token is the most secure option. I advise it especially for email, as mail is the root of your identity online. When your mail account is compromised password resets for a lot of services are childsplay.
Now there are also lots of tokens on the market. Such as the titan security key, and the onlykey. I decided to go with the Yubico brand because they implemented a lot of authentication options.
I have the following devices to play with:
YubiKey C Nano FIPS (USB Type-C form factor)
YubiKey 5 Nano (USB Type-A form factor)
YubiKey 5 NFC (USB Type-A form factor)

Yubikey uses FIPS 140 levels as explained here. Nice feature of the Yubikeys is the tamper-evidence coating. If it occurs you should be able to see that your device is tampered with. Another strong feature is that when trying to get to the cryptographic module the device will effectively break.
Yubikey 2FA/MFA
Over the past couple of months I started using Yubikeys for hardening my online posture and incorporating 2FA with every possible service. Luckily there are many sites and services that support USB-Dongle Authentication.
Please see this website which lists all sites using OTP (One Time Passwords) and/or U2F (Universal 2nd Factor).
I use the Yubikeys to store my GPG keys and sign my commits, and I use the hardened ssh-agent (what’s really cool is that openssh 8.2 is released that supports the Yubikey tokens out of the box).
Questions may arise. For example: why not use an authenticator app, or sms based 2FA? Simply because it is less secure. It might be “ok” for online services that are of lesser importance, but when we are talking about for example e-mail make no concessions. Secure it as much as you can because e-mail is the root of your online identity . When this account is compromised password resets can be done for a lot of services you registered for.
Checking the Yubikeys
The first thing you want to do is verify the genuinity of your Yubikeys: https://www.yubico.com/genuine/
If you want to check this manually, find out how to do that here.
Installation of Yubikey-manager software
Installation is covered here:
sudo apt-add-repository ppa:yubico/stable sudo apt update sudo apt install yubikey-manager-qt
Easy. With the Yubikey manager you now can configure different features of your devices. For example: I switched off the One Time Passwords.
Setup GPG keys
For this I followed a very good guide located here:
https://github.com/drduh/YubiKey-Guide
It will guide you through all the steps of generating a masterkey and creating subkeys and move them to Yubikey. Except for the master key itself. That should be saved offline in a safe place.
When you’ve followed the steps you should now have a subkey for signing [S], encrypting [E] and authentication [A] on your Yubidevice:
gpg -K /home/michel/.gnupg/pubring.kbx ------------------------------------ sec# rsa4096 2020-04-13 [C] D123E4C05FDD678987654A3F03ED4EAA4D0FB7E93 uid some-uid mails. ssb> rsa4096 2020-04-13 [S] [expires: 2021-04-13] ssb> rsa4096 2020-04-13 [E] [expires: 2021-04-13] ssb> rsa4096 2020-04-13 [A] [expires: 2021-04-13]
The # after the master key indicates it is deleted.
The > after the subkeys indicate it is only available on the Yubikey.
Password manager configured with Yubikey
I am not really fond of password managers that sync stuff to the cloud, I prefer a local manager like keepassxc. Installing keepassxc on Ubuntu should be straightforward. You can use the standard Ubuntu-repo’s or install it with snap.
If you install it with snap, don’t forget to run:
sudo snap connect keepassxc:raw-usb core:raw-usb
Configure your Yubikey manager: Applications > OTP > Long touch (slot2) keepassxc: Database > Change Master key > Add additional protection.
The Yubikey-manager also comes with the cli ykman tool, so you can:
List Yubikeys
ykman list YubiKey FIPS [OTP+FIDO+CCID] Serial: 1234567
Find info about your Yubikey
ykman info Device type: YubiKey FIPS Serial number: 1234567 Firmware version: 4.4.5 Enabled USB interfaces: OTP+FIDO+CCID Applications OTP Enabled FIDO U2F Enabled OpenPGP Enabled PIV Enabled OATH Enabled FIDO2 Not available
When you have multiple Yubikeys inserted, you have to use the –device flag:
ykman --device 1234567 info
Use of NFC Yubi 5 key
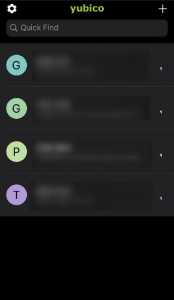
With this Yubikey it is possible to install a Yubico authenticator app on your NFC enabled phone. With it you can use multiple services in one application. Very nice.
After you add the services you want to use the Yubikeys with, you can then easily generate 2FA codes by refreshing it, and tapping the Yubikey NFC device in your phone:
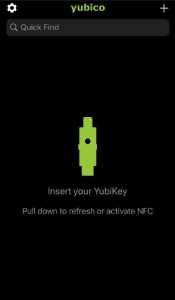
And all the 2FA codes are generated:
Ditch SFA forever
There are many more features when using the Yubikey, for example, the Yubikey PAM module. So there is still a lot to figure out 🙂 But for now, first things first, say bye bye to Single Factor Authentication & stay safe!






